Every business collects and stores personal information on both employees and customers. This data includes phone numbers, national insurance numbers, passwords, medical records, credit card and bank account numbers. If a business experiences a data breach, the resulting fallout can be catastrophic.
The consequences of having data compromised can extend beyond financials. They may cost a business its reputation and could possibly result in legal proceeding. And no organisation is immune, with large businesses such as Uber having also suffered data breaches over the years.
According to the 2022 IBM Cost of a Data Breach Report, the finance industry had the second highest cost per breach, averaging $5.97 million per breach. With cybercriminals becoming ingenious in their approach, it is expected that cybercrimes will continue to be on the rise. Cybersecurity Ventures expects global cybercrime costs to grow by 15 percent per year over the next five years, reaching $10.5 trillion USD annually by 2025, up from $3 trillion in 2015. This estimation is based on historical cybercrime figures including an increase in organised state-sponsored hacking activities and recent year-over-year growth.
How should a business respond to a data breach?
Putting a response plan in place prior to a data breach can make all of the difference. To ensure compliance, the General Data Protection Regulation (GDPR) requires that all businesses have organisational and technical data protection procedures. Having a data breach response plan ensures everyone understands what to do and how to go about it. In creating an effective data incident plan, here are 6 stages to consider:
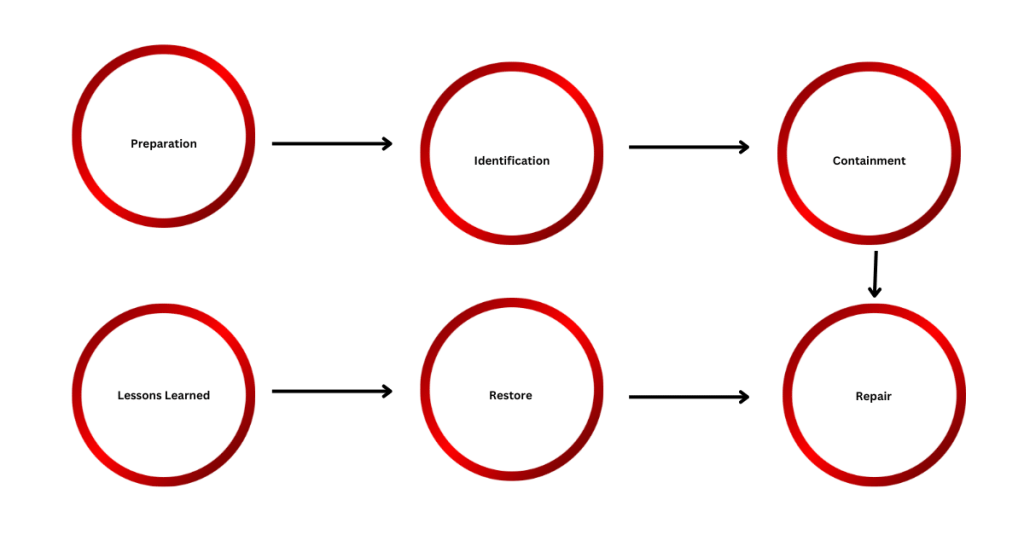
· Preparation
· Identification
· Containment
· Repair
· Restore
· Lessons Learned
1) Preparation
The preparation stage is vital in creating an effective plan. In this stage, simulated incident tests must be conducted and carefully analysed. This allows businesses to create a carefully constructed Incident report that allocates responsibilities to the most appropriate stakeholder. Incident Response plans should also take into cognisance the IR resources such as network diagrams, port lists, etc., that an organisation has at its disposal. This analysis should culminate in the preparation of an IR Tool Kit that is readily available for use in the event of a breach.
2) Identification
Businesses must ensure that defences that can immediately indicate compromise are in place. Identifiers of compromise may include unusual outbound network traffic, increased database read volume, new admin users created, unexpected patching, geographical irregularities, suspicious system file changes or registry, signs of DDOS activity, etc.
3) Containment
Once a business puts in defences that may indicate compromise, the next step must be allocating defined courses of actions based on the potential impact of various incidents. The organisation’s IT system needs to examine if it has control of certain aspects such as blocking of dangerous email and IP addresses, blocking of unauthorised access, and isolation of systems on the network. This ensures that the IT function has complete control and visibility of such actions.
4) Repair
Eliminate the cause of the breach. Safeguard must be implemented, malware deleted, breached user account disabled, firewalls rules updated, software patched, etc, to prevent a recurrence of the breach. Depending on the magnitude of the breach, your technical team can also contact relevant parties to advise on the breach. Together, they can work to fix any vulnerabilities.
5) Restore
In this phase, all recovery processes must be reviewed to ensure the restoration of the system as soon as possible. This phase must also consider validating that systems are back to being fully operational. Additionally, external penetration tests may be carried out to confirm that the restored fixes are sufficient.
6) Lessons Learned
This is a very important phase as lessons learned may go a long way in preventing a future breach. Audit to understand what has happened and put in measures to prevent future breaches. Measures may involve implementing new security measures, improving your employee training programs and regular security audits.
How quickly should a data breach be reported?
Notify appropriate parties
UK-based businesses must report any data breach to the Information Commissioner’s Office (ICO) within 72 hours of becoming aware of the incident, except it can be demonstrated that the breach is unlikely to result in a risk to individuals’ rights and freedoms. Data breaches can also be reported to the National Cyber Security Commission, although it is not a requirement. The NCSC offer free and confidential real-time threat analysis, defence against national cyber attacks and technical advice on cybersecurity. It is important to work with legal counsel to ensure compliance with applicable laws and regulations.
Businesses outside the UK must follow all state reporting laws to avoid penalties and further legal troubles.
While this is ongoing, a business must also do the following:
Notify affected persons
Article 34(1) GDPR. Communication of a personal data breach to the data subject states that “when the personal data breach is likely to result in a high risk to the rights and freedoms of natural persons, the controller shall communicate the personal data breach to the data subject without undue delay.”
Depending on the magnitude of the breach and whether or not it poses any risks to the rights and freedoms of your customers, it is critical to notify affected persons immediately and make them aware of the incident. This may include third-party vendors or partners who may have been impacted by the breach.
Communicate transparently with affected parties
Once an investigation has been completed and the cause of the breach ascertained, communicate transparently with affected customers. Provide a detailed explanation on the cause of the breach. This should include what data was compromised and what steps are being taken to prevent a future recurrence. It is important to communicate transparently and honestly about the situation, as this may help you build trust with your customers.
Preventing data breaches
While data breaches can be incredibly damaging, adopting a right response approach can minimise the impact and rebuild trust with your customers.
Tivarri’s Cranberry Cloud and Cranberry Desktop are configured to ensure that your critical digital information and assets are protected against both internal and external threats. We deploy a variety of cybersecurity services including multi-factor authentication, email security, web filtering, anti-virus, conditional access policies, end-to-end encryption, mobile device management, to keep your business safe. In addition to deploying the best-in-class technology, we can provide a training service that educates your employees on the steps required to ensure that your business is fully protected from cyber threats. Email us at [email protected] for more information.
